RDP Port Change vs Open Port 25: Complete Guide to Secure VPS Access and Reliable Email Setup
In today’s environment, VPS usage has grown rapidly. Whether you are managing websites, running automation workflows, hosting applications, or accessing a remote Windows system, understanding RDP port change and port 25 VPS configuration is essential for maintaining both security and functionality. VPS gives you flexibility and control that shared hosting cannot match, but only if it is properly configured.
However, most VPS environments come with default settings that are not optimized for real-world usage. In many cases, users ignore RDP port change and port 25 VPS issues during the initial setup, which later leads to security risks and email delivery problems. These defaults are designed to make setup easy, not secure.
As a result, users often face issues that directly impact performance and reliability, especially when they don’t properly manage RDP port changes and port 25 VPS settings. Understanding and fixing these areas early can significantly improve your server’s stability and protection.
The two most common problems VPS users encounter are:
- The default RDP port 3389 is exposed to the internet
- Email sending fails because port 25 is blocked
At first glance, these issues seem unrelated. One affects remote access, while the other affects email delivery. But both are deeply connected through how ports are configured and managed on a server.
Understanding these two areas is important if you want a stable and secure VPS setup. Without this knowledge, users often take incorrect steps like trying to force port 25 open or ignoring RDP exposure risks.
In this guide, we will break down both topics in a practical way. You will learn not only how to fix these issues but also the reasoning behind them, so you can make better decisions in the future.
Understanding the Role of Server Ports (Clear the Foundation)
Every service on a server communicates through a specific port. These ports act as endpoints that handle incoming and outgoing data.
You can think of ports as doors. Each service has its own dedicated door through which it communicates:
- Port 3389 → Remote Desktop Protocol
- Port 25 → SMTP
- Port 80 → HTTP
- Port 443 → HTTPS
When a port is open, it means that door is accessible to external systems. This is necessary for functionality but also introduces risk because anyone can attempt to connect.
When a port is closed or restricted, it improves security but may limit functionality.
This creates a constant balance between accessibility and protection. Proper port management is about controlling which services should be exposed and which should remain restricted.
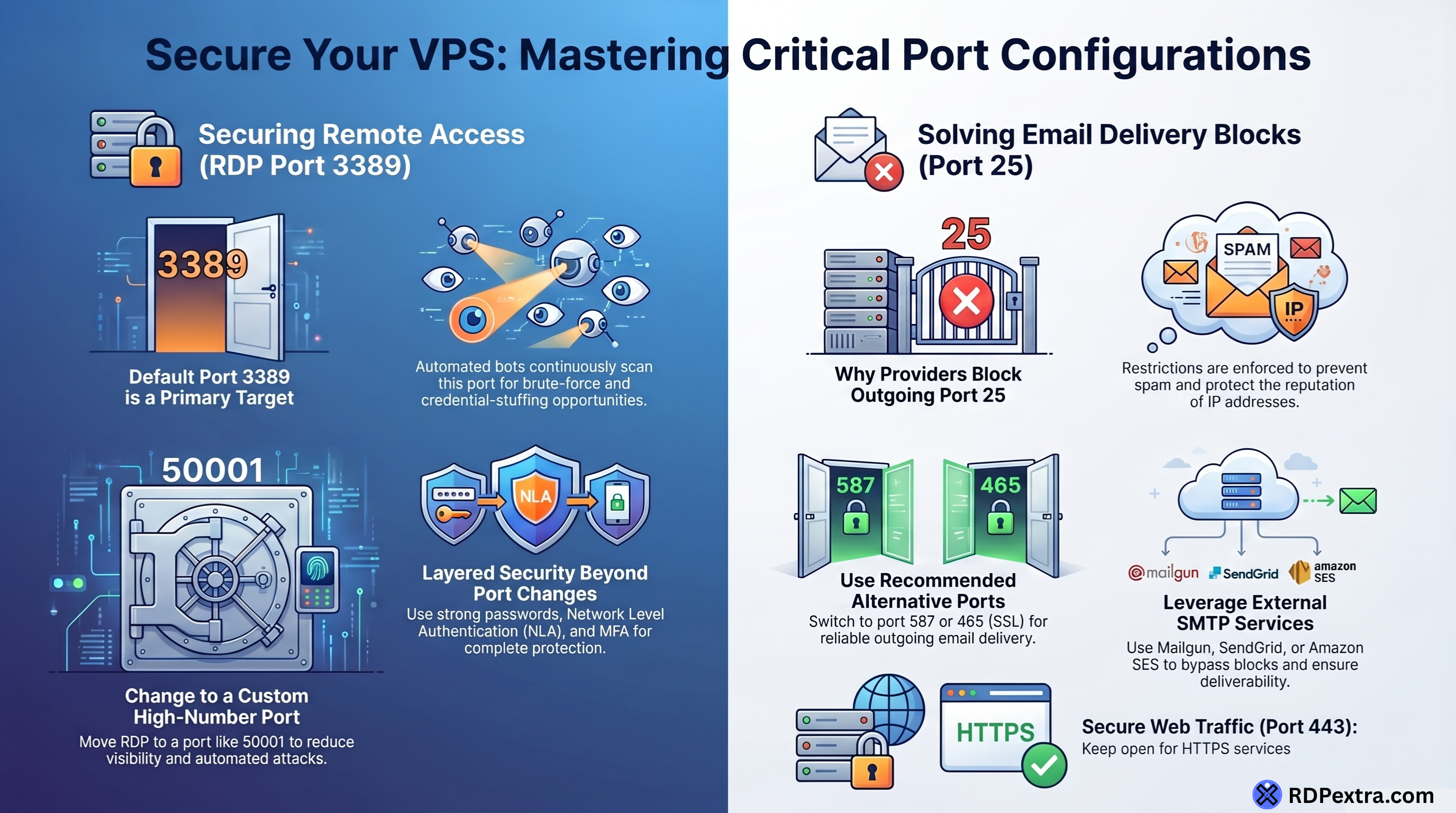
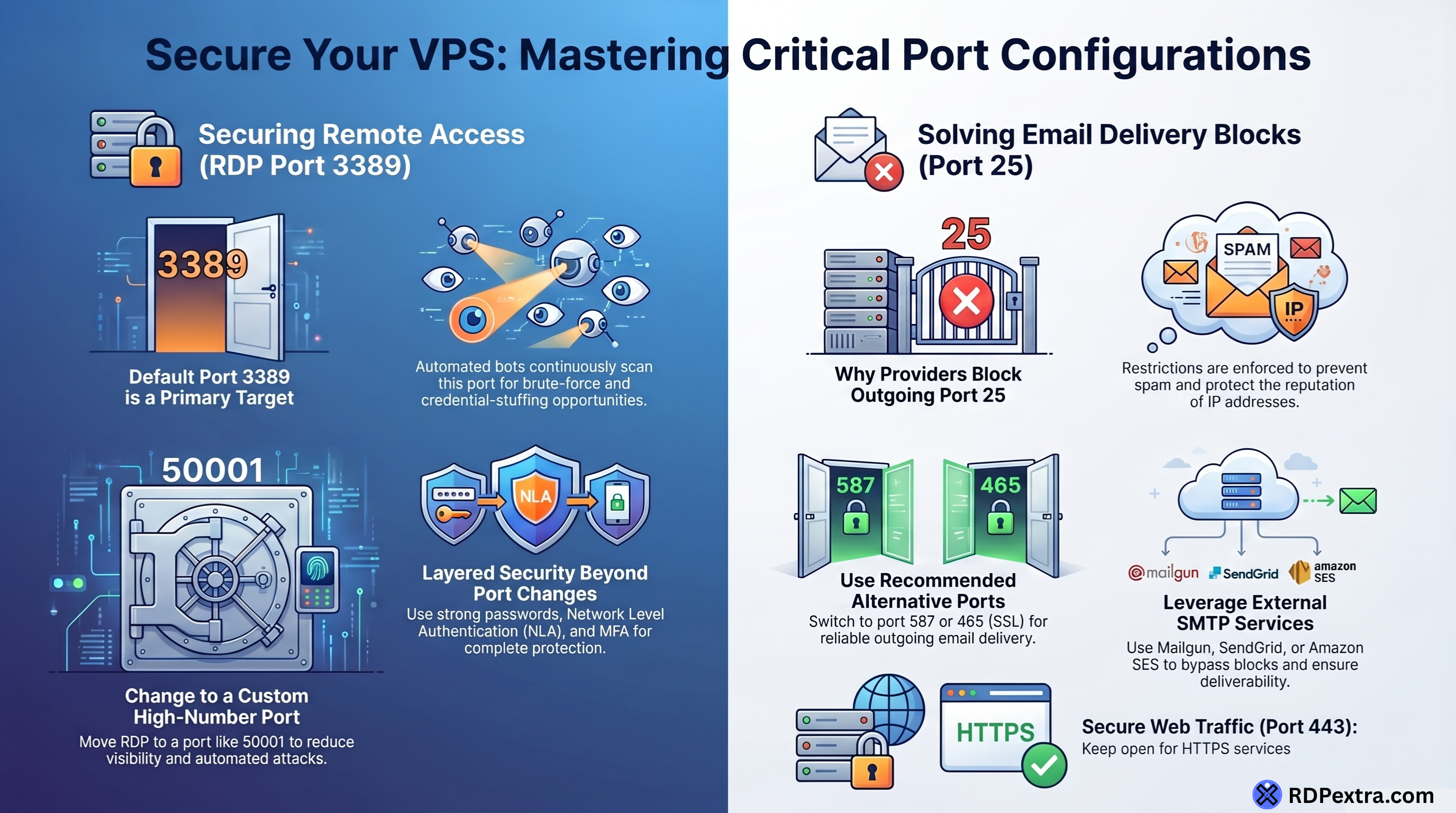
Default RDP Port (3389) – Primary Target for Attackers
What is the Real Problem?
Remote Desktop Protocol uses port 3389 by default. This is widely known across the internet, making it one of the first targets for automated attacks.
Attackers do not manually search for systems. Instead, they use bots that continuously scan IP ranges looking for open RDP ports. Once detected, these bots automatically attempt:
- Brute-force login attempts
- Username and password combinations
- Exploiting weak configurations or outdated systems
This process runs continuously. Even a fresh VPS can start receiving login attempts within minutes of going online.
If you check your server logs, you will likely see multiple failed login attempts from unknown IP addresses. This is a direct result of leaving port 3389 exposed.
Why Changing the RDP Port Matters
Changing the RDP port reduces visibility. Instead of using the default port, you move the service to a custom port that is not commonly scanned.
When you change port 3389 to something like 50001:
- Basic automated bots fail to detect your RDP service
- Random attack attempts drop significantly
- Your system becomes less visible in standard scans
This does not stop advanced attackers, but it filters out a large percentage of automated threats.
Real-World Impact of Port Change
In real-world scenarios, users who change their RDP port notice clear improvements:
- Fewer unauthorized login attempts
- Cleaner security logs
- Reduced system load from unwanted traffic
This simple adjustment improves overall server hygiene and reduces noise in monitoring.
RDP Port Change – Detailed Practical Steps
1. Registry Access and Backup
- Press Run → type
regedit - Export your registry settings before making changes
This ensures you can restore your system if needed.
2. Navigate to the Correct Path
HKEY_LOCAL_MACHINE\System\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp
Locate the PortNumber value.
3. Modify PortNumber
- Open
PortNumber - Change Base to Decimal
- Enter a new port number (e.g., 50001 or 49160)
Choose a high-numbered port to avoid conflicts with other services.
4. Firewall Configuration
- Open Windows Defender Firewall
- Create a new inbound rule
- Allow the new port
Without this step, your RDP connection will fail.
5. Restart the Server
Restart is required for changes to take effect.
Connecting After Port Change
To connect, specify the port along with the IP:
IP:PORT
Example:
192.168.1.10:50001
Strengthening RDP Security Beyond Port Change
Port change is just the first layer. A properly secured RDP setup includes multiple protections:
- Use strong and unique passwords
- Enable account lockout policies
- Enable Network Level Authentication (NLA)
- Use Multi-Factor Authentication (MFA)
- Restrict access using firewall rules
- Use a VPN for remote access
Layered security ensures better protection against both automated and targeted attacks.
Port 25 Blocked – Another Common VPS Issue
Real Scenario
You configure a mail server on your VPS, everything seems correct, but emails fail to send.
In most cases, the issue is:
Port 25 is blocked
Understanding the Role of Port 25
SMTP uses port 25 for traditional email communication.
It is mainly responsible for:
- Sending emails between servers
- Handling outgoing mail delivery
However, due to widespread misuse, its role has changed in modern hosting environments.
Incoming vs Outgoing Traffic Explained
- Incoming traffic (receiving emails) → usually allowed
- Outgoing traffic (sending emails) → often restricted
This means your server can receive emails but cannot send them directly using port 25.
Why Hosting Providers Block Port 25
1. Spam Prevention
Spam is one of the biggest issues on the internet. Opening port 25 makes it easy for malicious users to send bulk spam emails.
2. IP Reputation Protection
If spam is detected from a server:
- The IP gets blacklisted
- Email delivery fails across platforms
- Entire IP ranges may be affected
3. Infrastructure Stability
Uncontrolled email traffic can overload servers and networks.
4. Legal and Compliance Requirements
Providers must follow anti-spam laws and regulations, making port blocking necessary.
Practical Solutions for Email Sending
External SMTP Services
- Mailgun
- SendGrid
- Amazon SES
These services handle:
- Email delivery optimization
- Spam filtering
- Reputation management
Alternate SMTP Ports
Instead of port 25:
- 587 (recommended)
- 465 (secure SSL)
These ports are widely supported and suitable for sending emails.
Requesting Port 25 Access
Some providers allow requests, but:
- Approval is strict
- Requires business justification
- Not always granted
Connecting the Dots: Security and Control
Both topics revolve around one concept:
Controlled access
- RDP port change controls inbound access
- Port 25 blocking controls outbound activity
Together, they help maintain a secure and stable server environment.
Advanced VPS Management Practices
For long-term efficiency:
- Regularly monitor logs
- Keep software updated
- Minimize exposed services
- Use intrusion detection tools
- Separate email infrastructure from VPS
Proactive management reduces risks and improves stability.
Conclusion
A well-managed VPS is not just about performance but about maintaining a balance between usability and security.
- Changing the RDP port reduces exposure to attacks
- Blocking port 25 prevents misuse and protects the network’s reputation
When these practices are combined with proper monitoring and configuration, your VPS becomes significantly more secure and reliable.
Taking the time to understand and implement these changes ensures long-term stability and better control over your server environment.
